Presence verification for irreversible actions · exportable evidence
If it can’t be undone, it must be presence-verified.
PBI is a drop-in presence layer for high-risk systems. Bind a WebAuthn challenge to an action hash, require a live UP+UV ceremony (FaceID / TouchID), and receive a signed, non-replayable receipt — plus optional portable proof bundles for offline verification, audit, and chain-of-custody.
Presence-bound verification in under a minute.
Action-bound proof
Receipts bind presence to the exact operation you intended to perform.
Non-replayable by design
Single-use challenges stop replays, scripts, and delegated approvals.
Portable evidence
Export PBI Packs/Proofs for offline verification, audits, and disputes.
No identity database
Verify presence without storing users, passwords, or biometrics.
Built for teams who can’t afford “maybe” approvals
Treasury & payoutsAdmin control planesGovernance & multisigDeploy & production changesLegal / ownership actions
Trust & operations
Proof in under a minute
Run the live presence ceremony
The demo shows the full ceremony end-to-end. The tool is an integration harness (BYOK) for real API keys, real action hashes, and receipt/proof debugging.
Recommended
Plan
Live Demo
Free
Public-safe demo. No API keys. Runs the full ceremony.
Best for: buyers, security reviewers, engineers validating the flow.
•No keys required
•Register passkey → attest → verify
•Receipt minted + decision shown
•Safe to share in public
Plan
Attester Tool
BYOK
Integration harness for real keys and real API bases.
Best for: customers integrating PBI into production endpoints.
•Use your real API key
•Custom action payload + actionHash
•Receipt hashes + portable proofs
•Requires portal account
Plan
Developer Hub
Start
Quickstart, patterns, canonicalization and enforcement guidance.
Best for: teams integrating PBI into real endpoints.
•5-minute quickstart
•Action hashing guidance
•Enforcement patterns
•Links to reference docs
Plan
API Docs
Read
Exact endpoints, payloads, and response semantics.
Best for: implementation + security review.
•/v1/pbi/challenge
•/v1/pbi/verify
•/v1/pbi/receipts?createdAfter&order&cursor
•/v1/pbi/receipts/{receiptId}
•/v1/pbi/receipts/export
•/v1/portal/webhooks
•Auth: Bearer API key
•Receipt + pack/proof model
Why PBI exists
From account trust → human presence proof
Passwords, sessions, and tokens prove only that something authenticated. PBI proves a human was physically present and authorized the exact action you care about — then exports a proof you can verify later.
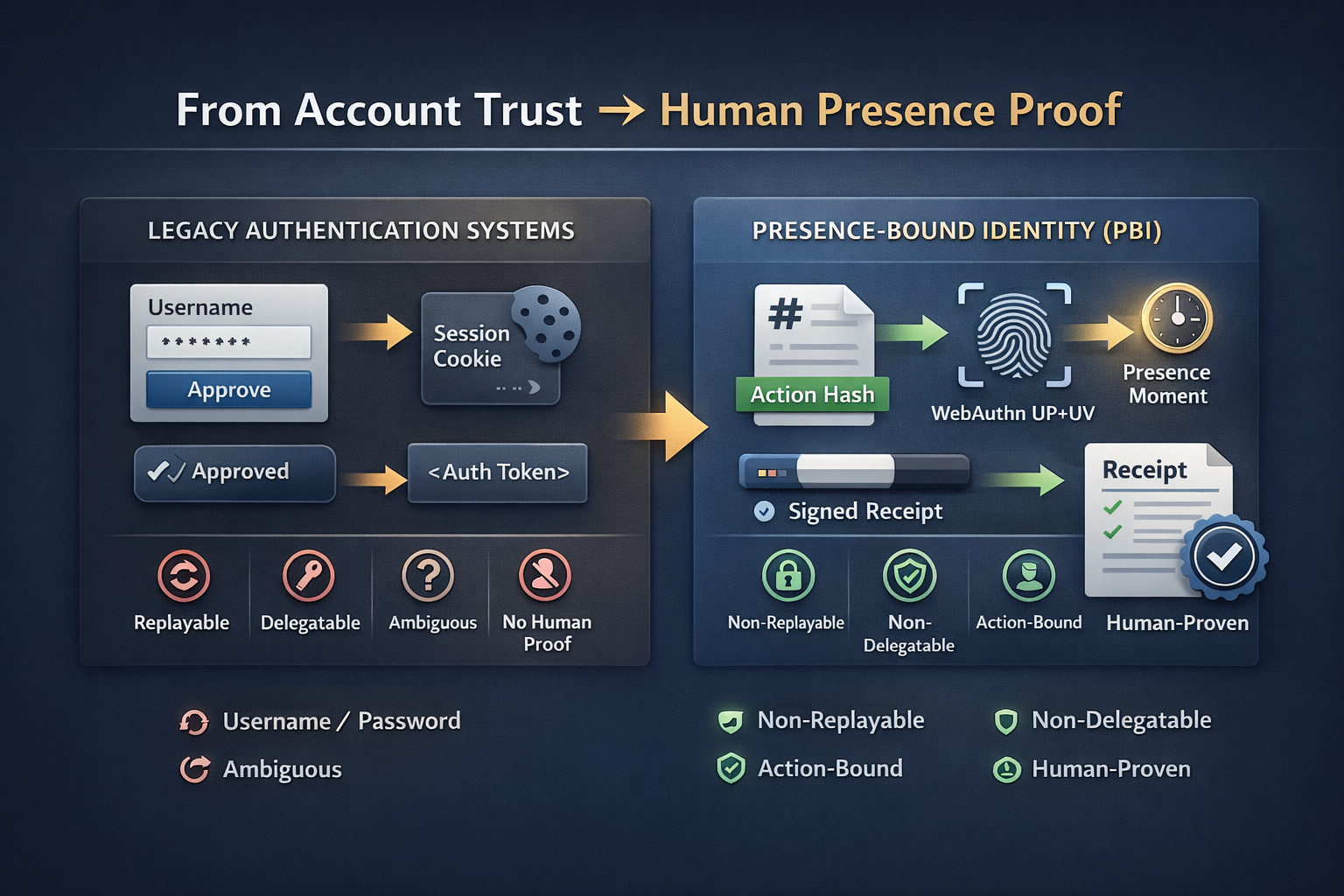
Legacy auth answers “who has access?” PBI answers “was a human present for this exact irreversible action?”
Mechanism
Presence verification is a simple, strict flow
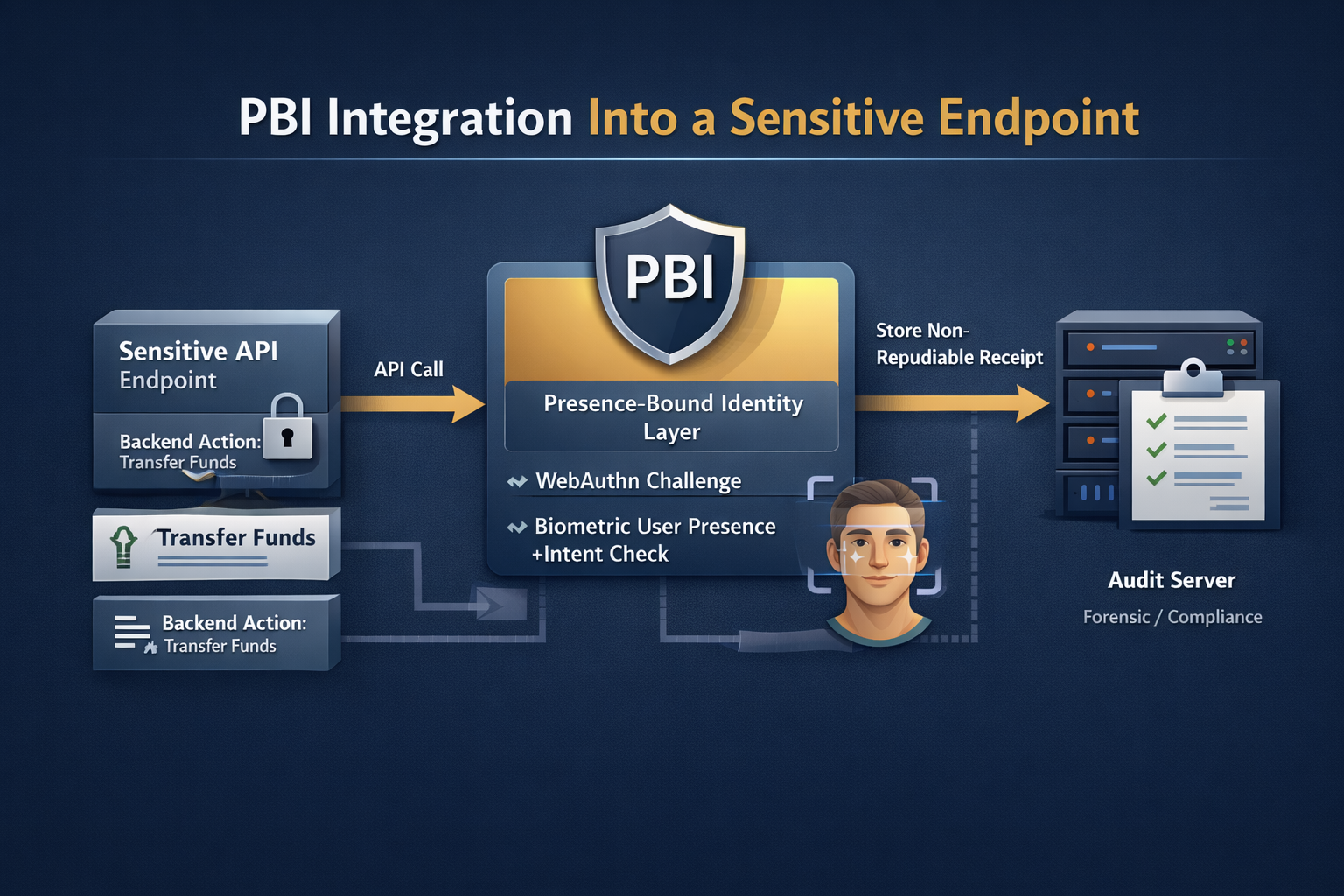
Hash the action, issue a challenge bound to that hash, require UP+UV, then store the receipt. If verify doesn’t return PBI_VERIFIED, you do not proceed.
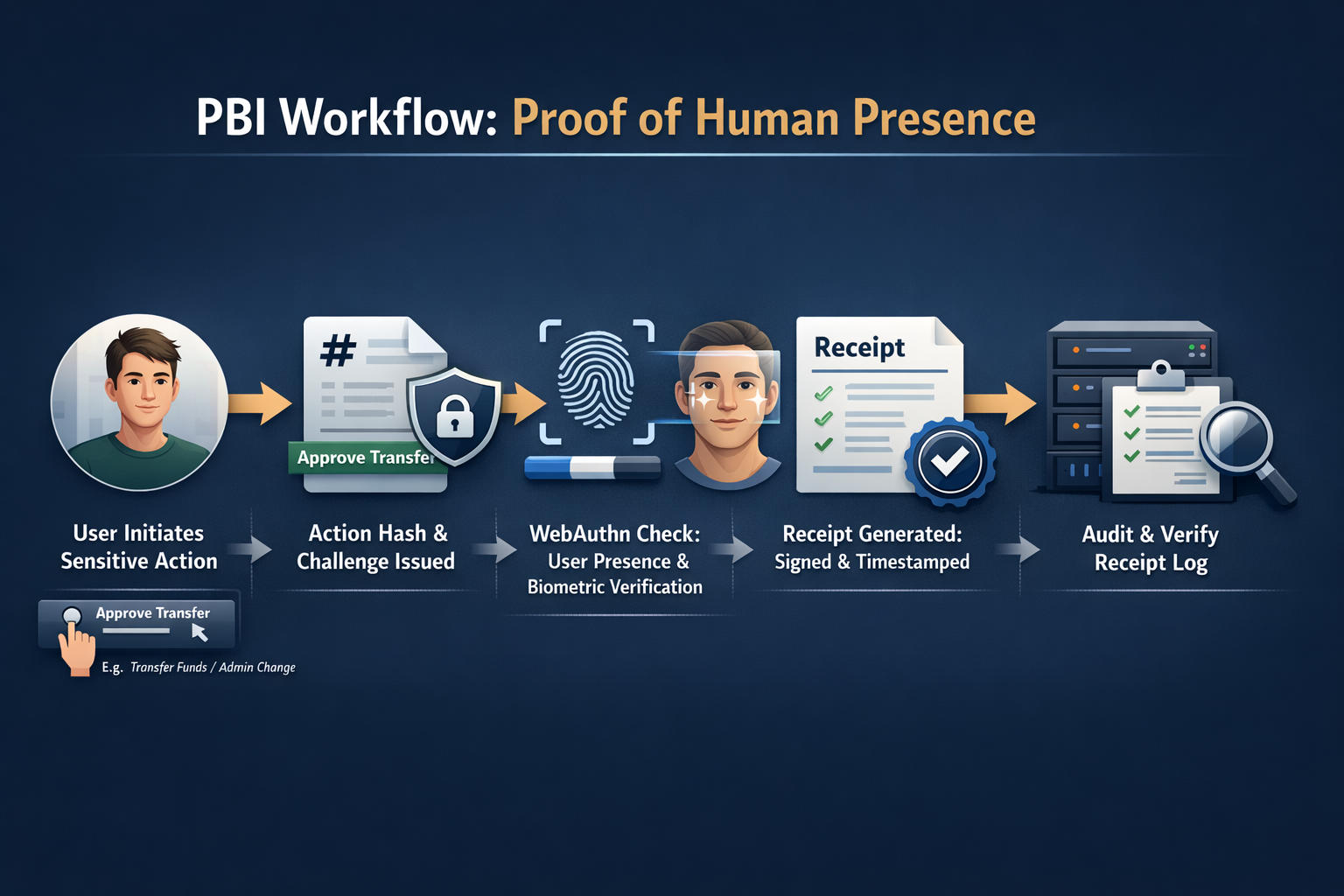

1) Bind the action
Hash what you’re about to do (transfer, rotate keys, deploy). Challenge is bound to that hash.
2) Prove presence (UP+UV)
User completes a live WebAuthn ceremony. No accounts required for the proof.
3) Enforce + store receipt
Proceed only on PBI_VERIFIED. Store receipt hash for audit, forensics, disputes.
Offline verification (optional)
For audits and custody chains, PBI can export a signed pack/proof that verifies offline under a trust policy (rotation/revocation/expiry).
pbi-pack-verify ../pbi-pack --trust ./trust.json pbi-pack-verify --proof proofs/0001.proof.json --trust ./trust.json
Where it belongs
If it can’t be undone, it must be presence-verified
PBI is for operations where “approved” must mean “a human was physically present and knowingly authorized it.”
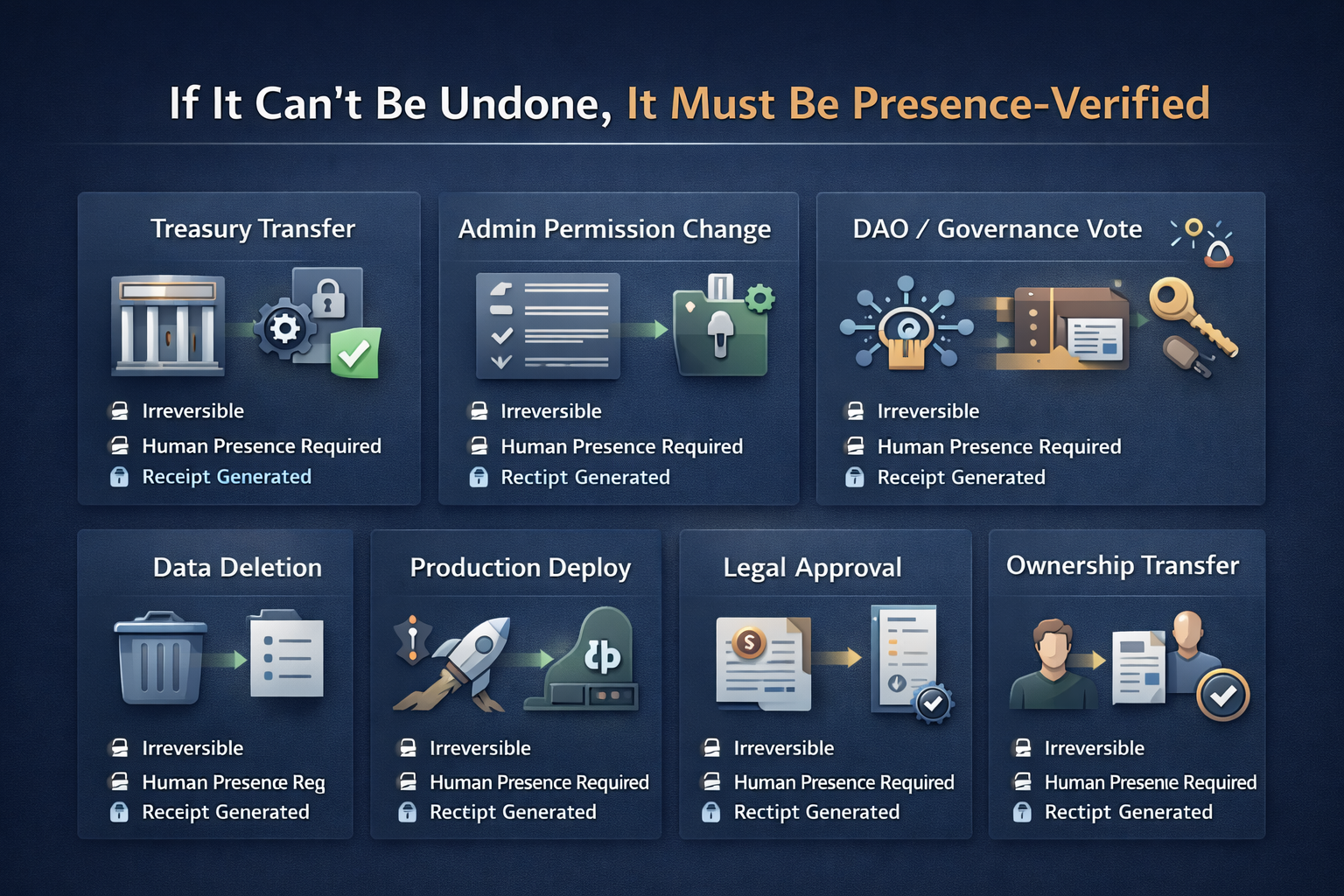
Common enforcement points
Wrap the endpoints that move money, change control, or create irreversible commitments.
Treasury & transfers
Presence-gate wires, payouts, escrow release.
Admin & access control
Gate role changes, key rotations, deploy approvals.
Governance actions
Gate votes, proposals, multisig flows.
Authorship confirmation
Presence-stamp contracts, releases, publications.
Critical config changes
Gate flags, production settings, incident actions.
High-risk user actions
Gate recovery, withdraw, device enrollment.
Evidence layer
The PBI receipt: proof, not logs
Logs are mutable, incomplete, and rarely dispute-ready. A receipt is cryptographic evidence: action-bound, timestamped, single-use, and verifiable long after the event.
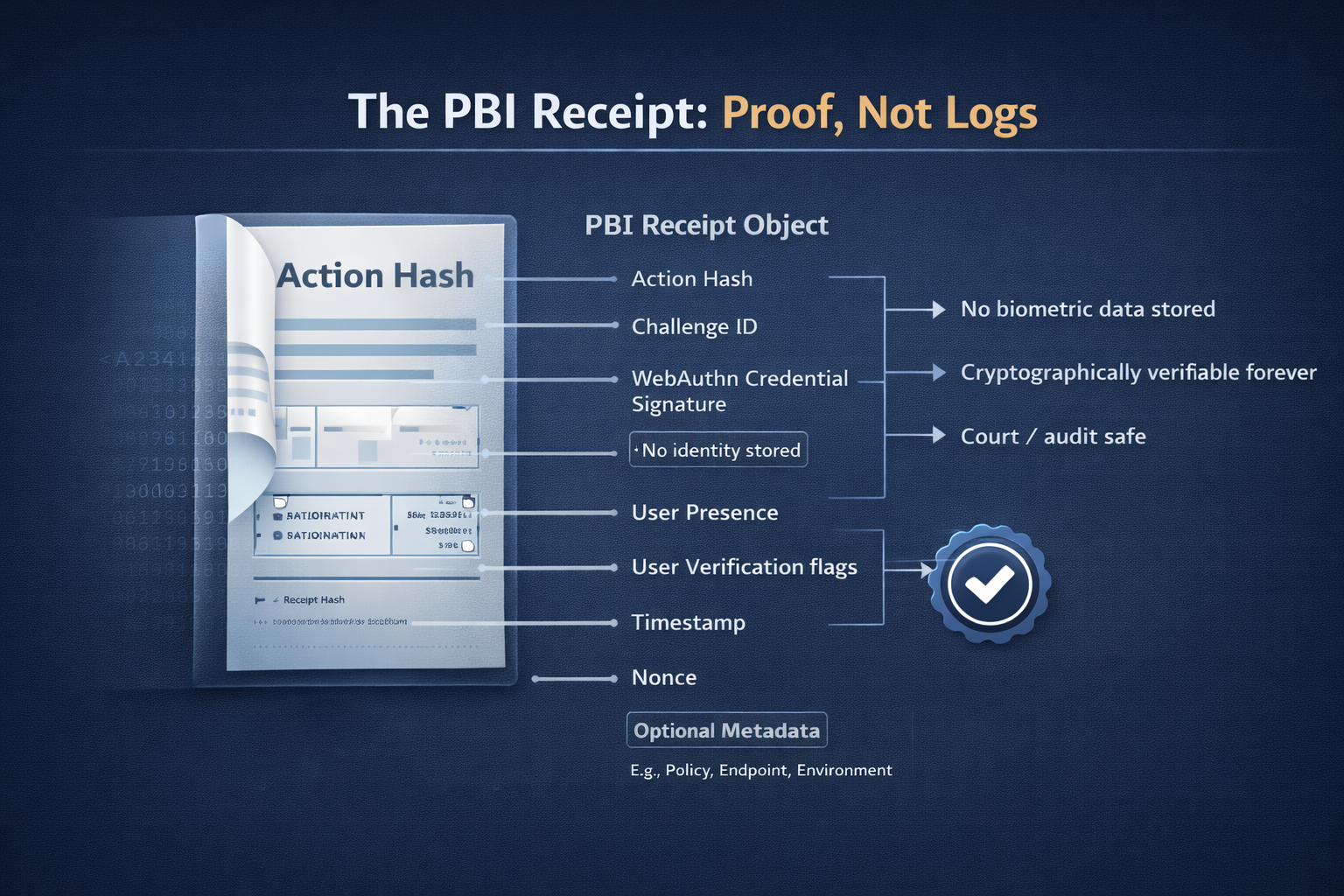
No biometric data stored. No identity stored. Receipts remain verifiable.
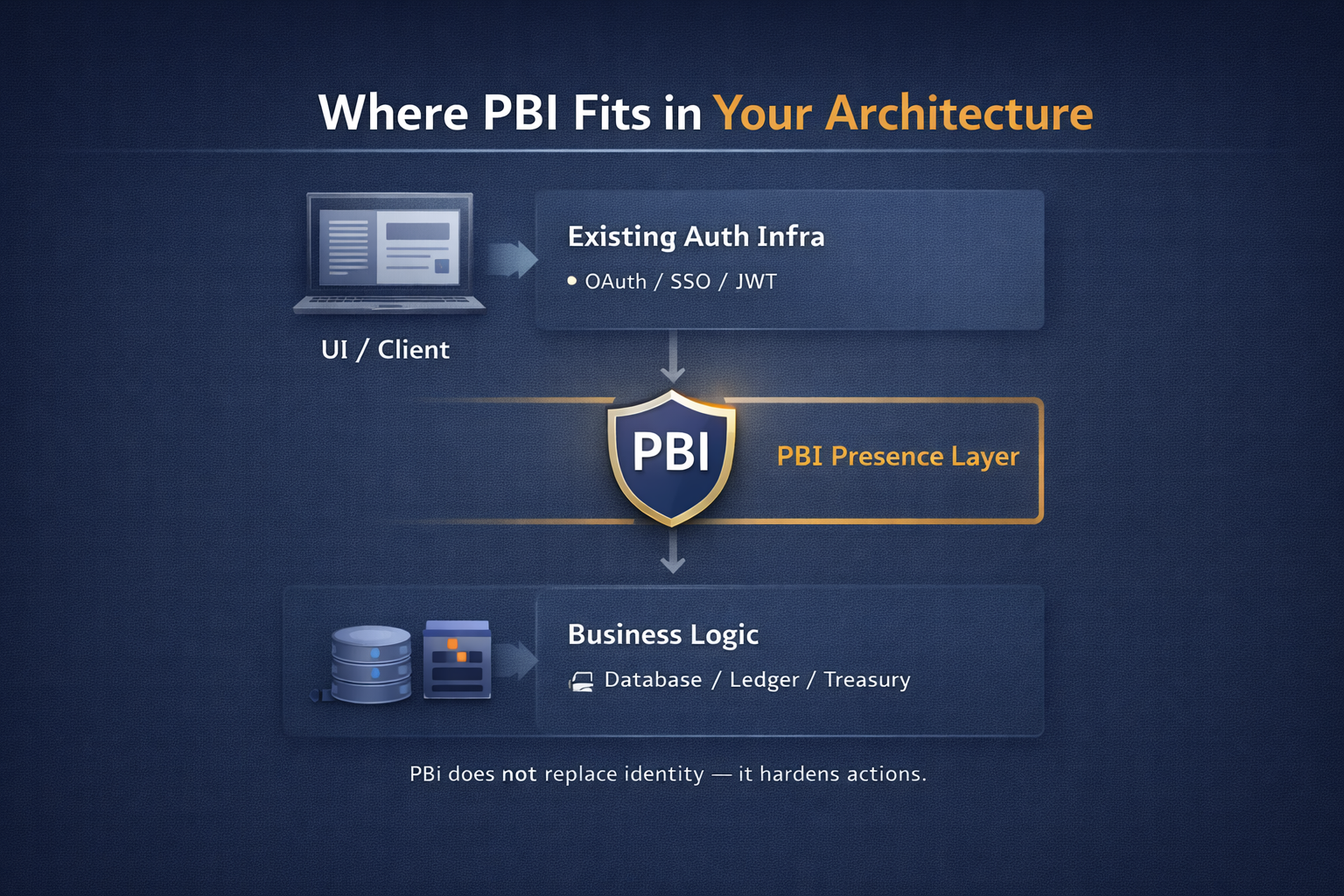
Integration
PBI does not replace identity — it hardens actions
Keep your existing auth (SSO/OAuth/JWT). Add PBI only where you need cryptographic proof of human presence for irreversible operations.
Pricing
Choose your verification capacity. Usage is metered automatically. A “verification” is one successful /v1/pbi/verify returning PBI_VERIFIED.
Plan
Starter
$99
/month
Ship presence gates fast.
Best for: teams shipping their first high-risk presence gates.
•Presence verification core
•Includes 10,000 verifications/mo
•Receipt hash + audit trail
•Overage billed per verification (shown in portal)
Recommended
Plan
Pro
$499
/month
Higher throughput + more automation.
Best for: products scaling enforcement coverage.
•Everything in Starter
•Includes 100,000 verifications/mo
•Priority processing
•Overage billed per verification (shown in portal)
Recommended
Plan
Scale
$1,999
/month
Authoritative human presence at scale.
Best for: financial infrastructure, governance, mission-critical control.
•Everything in Pro
•Includes 1,000,000 verifications/mo
•Enterprise throughput + reliability
•Portable proofs for audit workflows
•Overage billed per verification (shown in portal)
Recommended
Plan
Enterprise (PBI Assured)
Talk to Sales
Procurement-ready. Governance support and enterprise guarantees.
Best for: banks, governments, platforms, custodians, and mission-critical control planes.
•Paid pilot available (1 endpoint, 2 weeks)
•Custom verification capacity + burst
•SLA / priority support options
•Security review packet on request
•Trust policy + key rotation guidance
•Audit export & evidence bundling
Get access
Sign in with a magic link.
You’ll land in the client portal to activate billing, create API keys, and track usage. No passwords.
By continuing, you agree to the Terms and Privacy Policy.
For security reviewers
What PBI guarantees (and what it doesn’t)
PBI produces cryptographic proof of live human presence for a specific action. It does not attempt to identify who the user is, nor does it store biometric data.
Guarantee
UP+UV ceremony occurred for this action hash, single-use, within expiry.
Does not do
Identity resolution, KYC, biometric storage, or user databases.
Portable evidence
Optional PBI Packs/Proofs allow offline verification with rotation/revocation/expiry.
Operational model
challenge → verify → receipt; enforce only on PBI_VERIFIED.